For any organization handling digital personal data in India, understanding and implementing the DPDP audit process is no longer optional—it’s a strategic necessity. The Digital Personal Data Protection Act, 2023 (DPDP Act), India’s landmark privacy legislation, moves beyond setting rules to demanding demonstrable accountability. The ultimate question for regulators and stakeholders is no longer “Do you have a policy?” but “Can you prove your compliance?” This is where a systematic DPDP audit becomes critical. It is the definitive process to check, verify, and evidence that your data handling meets the law’s stringent requirements, safeguarding you from penalties that can reach ₹250 crore. Let’s break down this essential process from start to finish.
Why a DPDP Audit is Your Compliance Cornerstone
A DPDP audit is a structured, independent examination of your organization’s personal data processing activities against the obligations set forth in the DPDP Act and its 2025 Rules. Its purpose is twofold: to identify gaps that could lead to regulatory action and to create a verifiable record of your compliance posture.
Crucially, for organizations likely to be designated as Significant Data Fiduciaries (SDFs)—based on data volume, sensitivity, and risk—periodic independent data audits are a mandatory requirement under the Act. Even for businesses not classified as SDFs, a formal audit is the strongest evidence of good faith compliance, significantly influencing proceedings in your favor should the Data Protection Board of India (DPBI) ever inquire.
It’s vital to distinguish an audit from a gap assessment. A gap assessment is a preliminary diagnostic to see where you fall short; a compliance audit is the final verification that you have successfully closed those gaps and can be formally certified as compliant.
The 6-Phase DPDP Audit Methodology
A rigorous audit follows a phased approach, typically spanning 4 to 5 weeks for a mid-sized company, ensuring no stone is left unturned. Here is the complete breakdown:
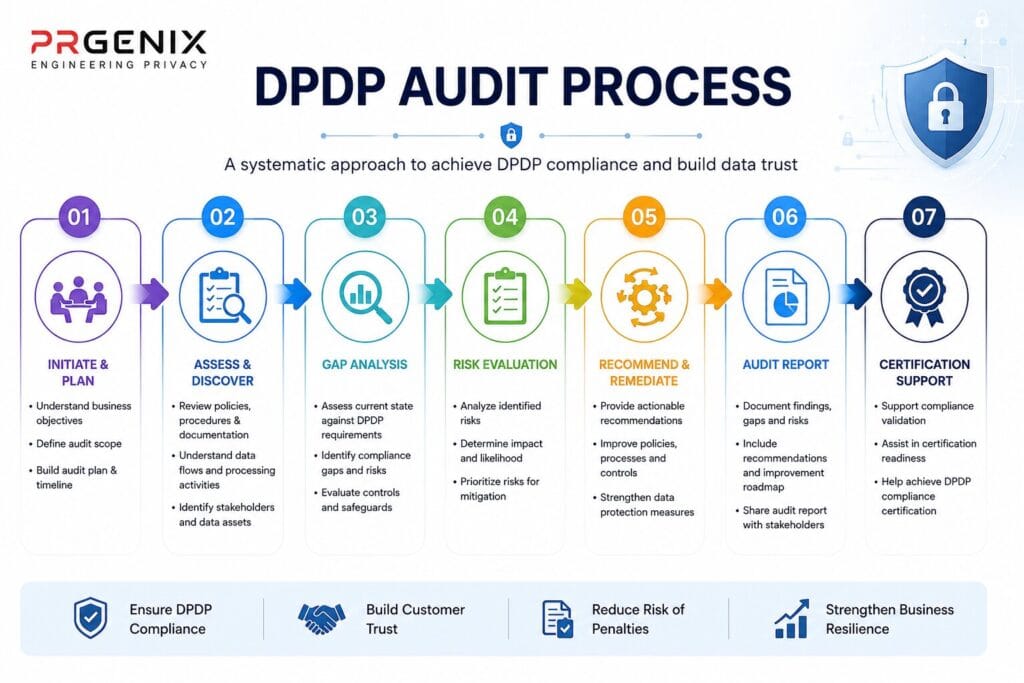
Phase 1: Scoping and Planning (Week 1)
Before the review begins, clarity on scope is paramount. This phase involves defining the boundaries of the audit: which entities, departments, data flows, and technology platforms will be examined. A critical step is assembling the right audit team, which should include:
- Audit Lead: A compliance officer or project manager to drive the timeline.
- Legal/Compliance Expert: To interpret DPDP requirements.
- Engineering/IT Representative: To map technical data flows and controls.
- Key Department Heads (HR, Sales, Marketing): To provide ground-truth on daily data handling.
Phase 2: Discovery and Documentation Review (Week 1-2)
This is the foundation of the audit, often the most labor-intensive part. The goal is to build a complete Personal Data Inventory and map all data flows. Auditors will:
- Identify Every Data Collection Point: From website forms and mobile apps to HR files and internal spreadsheets.
- Build a Detailed Inventory: For each system (CRM, HR software, marketing tools), document what data is collected, its purpose, legal basis (consent or legitimate use), retention period, and who it is shared with.
- Map Data Flows: Trace how personal data moves from collection through processing, storage, sharing, and eventual deletion, paying special attention to transfers to third-party processors.
Concurrently, auditors will conduct a Document Review of your privacy notice, internal data protection policies, data processing agreements (DPAs) with vendors, consent records, and past incident logs.
Phase 3: Assessment and Evidence Collection (Week 2-3)
With the inventory mapped, auditors assess your practices against specific DPDP mandates. This involves deep checks across several domains:
- Consent & Notice Compliance: Is consent free, specific, informed, and unambiguous? Is the privacy notice clear, standalone, and available in required languages? Are verifiable consent records maintained?
- Security Safeguards: Are “reasonable security safeguards” as per Section 8(4) implemented? This includes checks for encryption (in transit and at rest), access controls, audit logging, and vulnerability management.
- Data Principal Rights Fulfillment: Can individuals practically exercise their rights to access, correction, erasure, and grievance redressal? Auditors will test these processes end-to-end.
- Third-Party Risk Management: Are all data processors bound by compliant DPAs? Is there oversight of their security practices and sub-processors?
- Breach Preparedness: Is there a documented breach response plan that ensures notification to the DPBI and affected individuals “without unreasonable delay”?
Phase 4: Interviews and Technical Testing (Week 3)
Documentation tells what should happen; interviews and testing reveal what actually happens. Auditors will conduct structured interviews with the DPO, IT staff, and department heads to validate processes. They will also perform technical testing, which may include verifying access controls, reviewing system logs for unauthorized access, and testing the functionality of consent withdrawal mechanisms.
Phase 5: Analysis, Reporting, and Grading (Week 4)
Auditors consolidate findings into a severity-based report:
- Critical Findings: Direct violations of the DPDP Act requiring immediate resolution (e.g., no lawful basis for processing, absence of a mandatory DPO for an SDF).
- High-Risk Findings: Significant gaps that create material regulatory exposure (e.g., poor breach notification procedures, inadequate vendor contracts).
- Medium Findings: Areas for improvement that enhance compliance maturity (e.g., data retention schedules needing refinement).
- Informational Notes: Best-practice recommendations beyond minimum compliance.
The final report provides a clear roadmap for remediation, prioritized by risk.
Phase 6: Certification and Follow-up
Upon satisfactory resolution of critical findings, an independent auditor can issue a DPDP Compliance Certificate. This is a powerful tool for building trust with customers, partners, and regulators. Compliance is not a one-time event; schedules for annual recertification audits should be established to ensure ongoing adherence as your business and the regulatory landscape evolve.

Core Documents and Evidence Required for Audit Readiness
Being “audit-ready” means having your evidence organized. Regulators expect you to maintain and produce:
- Records of Processing Activities (ROPA): Your comprehensive data inventory.
- Consent Logs: Verifiable records of who consented, when, and to what.
- Privacy Notice & Internal Policies: DPDP-aligned and current versions.
- Data Processing Agreements (DPAs): Signed contracts with all third-party processors.
- Data Protection Impact Assessment (DPIA) Reports: For high-risk processing activities (mandatory for SDFs).
- Security Control Evidence: Reports on encryption, access reviews, and penetration testing.
- Data Subject Request Logs: Records of how rights requests were handled and fulfilled.
- Breach Response Plan and Incident Logs.
Common Pitfalls and How to Avoid Them
Organizations often stumble on the same hurdles:
- Incomplete Data Visibility: Underestimating how many systems and spreadsheets hold personal data.
Solution: Conduct a thorough, department-by-department discovery.
2. Weak Consent Mechanisms: Relying on bundled “Terms & Privacy” checkboxes.
Solution: Implement purpose-specific, clear consent capture with easy withdrawal.
3. Paper-Only Policies: Having policies that aren’t implemented in practice.
Solution: Combine documentation with training, testing, and technical enforcement.
4. Neglecting Vendor Risk: Failing to bind processors with strong DPAs.
Solution: Map all data flows to third parties and establish a vendor risk management program.
From Compliance Checkbox to Competitive Advantage
The DPDP audit process is more than a regulatory hurdle. It is a rigorous health check for your organization’s data ethics. By systematically understanding your data flows, fortifying security, and respecting individual rights, you not only mitigate the risk of catastrophic penalties but also build profound trust with customers and partners. In the data-driven economy of 2026 and beyond, that trust is the ultimate competitive advantage. Start your audit journey now—your due diligence today is your defense tomorrow.
ENSURE DPDP COMPLIANCE BEFORE IT BECOMES A LIABILITY
Protect your business from data privacy risks, regulatory penalties, and customer trust issues with professional DPDP Audit & Certification services by Prgenix.